
Want to get the most out of ChatGPT?
ChatGPT is a superpower if you know how to use it correctly.
Discover how HubSpot's guide to AI can elevate both your productivity and creativity to get more things done.
Learn to automate tasks, enhance decision-making, and foster innovation with the power of AI.


Confidential Computing Secures Data Even During Processing→Confidential computing is emerging as a major breakthrough in cybersecurity by protecting sensitive data while it is actively being processed, not just when stored or transmitted. The technology uses hardware-based Trusted Execution Environments (TEEs) that isolate workloads so even cloud providers or system administrators cannot access the underlying data. Major cloud vendors and security platforms are adopting confidential computing to enable secure AI development, data analytics, and cross-organization collaboration without exposing sensitive information.
Zero Trust Network Access Reshapes Enterprise Security Architecture→Zero Trust Network Access (ZTNA) is rapidly replacing traditional VPN-based security models by enforcing continuous verification for every user, device, and connection attempting to access corporate resources. Instead of assuming trust inside a network perimeter, Zero Trust frameworks authenticate and validate every request in real time using identity, device health, and behavioral signals. As organizations migrate workloads to the cloud and support distributed workforces, ZTNA technologies are becoming a cornerstone of modern enterprise cybersecurity architecture.
AI-Driven Threat Detection Platforms Identify Attacks in Real Time→Artificial intelligence is redefining cybersecurity operations by enabling systems to analyze massive volumes of network telemetry and detect anomalies automatically. AI-powered security platforms can identify suspicious behaviors, prioritize incidents, and initiate rapid responses before attackers gain a foothold. These solutions are increasingly used across enterprise networks, cloud environments, and SaaS platforms, helping security teams keep pace with modern threat actors.
Privacy-Enhancing Technologies Protect Sensitive Data Across Its Lifecycle→Privacy-Enhancing Technologies (PETs) are gaining traction as organizations seek ways to securely analyze and share sensitive data without exposing it. PET frameworks combine technologies such as secure multiparty computation, homomorphic encryption, and trusted execution environments to maintain confidentiality during analytics and collaboration. These tools are increasingly used in sectors such as healthcare, finance, and government where strict data protection requirements are essential.

Introduction
The modern internet has quietly developed a second economy beneath the visible surface. Beyond the familiar platforms of commerce, social media, and enterprise infrastructure exists a hidden digital marketplace where stolen credentials, compromised identities, and illicit cyber tools are traded with alarming efficiency. These underground environments—commonly referred to as dark web cyber-crime marketplaces—have evolved into sophisticated economic ecosystems that mirror legitimate online commerce. Vendors advertise products, buyers leave reviews, escrow systems facilitate trust, and administrators enforce marketplace rules. What was once a chaotic collection of hacker forums has transformed into an organized digital bazaar operating with remarkable professionalism.
The expansion of these marketplaces represents one of the most significant cybersecurity challenges of the modern era. Stolen usernames, passwords, corporate network access, financial information, and even entire digital identities are now treated as commodities. Criminal enterprises no longer require advanced hacking skills to launch attacks; they simply purchase access from those who specialize in harvesting it. The result is an industrialized cyber-crime ecosystem where specialization, automation, and global connectivity allow threat actors to scale operations with unprecedented reach. For cybersecurity professionals, understanding how these markets function is essential to defending against them.

The Architecture of the Underground Cyber-Crime Economy
Dark web marketplaces operate using infrastructure designed to conceal both buyers and sellers. Most are hosted on anonymizing networks such as Tor, which routes traffic through multiple encrypted layers, making it extremely difficult to trace participants or identify server locations. Access typically requires specialized browsers and knowledge of hidden service addresses that are intentionally difficult to discover. Once inside, the experience often resembles legitimate e-commerce platforms, complete with categorized listings, search functions, vendor profiles, and customer feedback systems.
Administrators of these platforms often enforce strict operational rules to maintain stability and credibility within the criminal ecosystem. Escrow payment systems ensure that funds are released only when buyers confirm the validity of purchased data. Cryptocurrency payments—typically using privacy-focused digital assets—allow transactions to occur without traditional financial oversight. Some marketplaces even provide customer support channels, dispute resolution services, and vendor verification programs to ensure that sellers provide legitimate stolen data rather than fabricated products. In essence, these platforms function as shadow versions of mainstream online marketplaces.
Operational Mechanics of Credential Harvesting and Distribution
The supply chain feeding these marketplaces begins with credential harvesting operations. Threat actors obtain usernames, passwords, and authentication tokens through several primary methods. Phishing campaigns remain one of the most effective strategies, where victims are tricked into entering login credentials on convincing but malicious websites. Malware infections also play a major role, particularly information-stealing malware designed to extract saved browser passwords, authentication cookies, and cryptocurrency wallet keys.
Once collected, this data is aggregated into massive databases commonly referred to as “combo lists.” These lists may contain millions—or even billions—of credential pairs gathered from multiple breaches. Vendors organize the data by service type, geographic location, or account value before listing them for sale on underground marketplaces. Some sellers specialize in “fresh logs,” meaning recently harvested credentials that have a higher likelihood of still being valid. Others offer bulk credential collections sold at extremely low prices, enabling buyers to test large volumes of accounts through automated credential stuffing attacks.
Effectiveness and Profitability of Credential Based Cyber-Crime
The reason these marketplaces continue to expand is simple: the business model works. Credential-based attacks remain one of the most successful forms of cyber intrusion because users frequently reuse the same passwords across multiple services. When attackers obtain login information from one breached platform, they can attempt those credentials across hundreds of other websites, including corporate systems, banking portals, and cloud services. Even a small success rate can yield valuable access.
From a financial perspective, the economics strongly favor the attackers. Individual login credentials may sell for only a few dollars, but access to high-value accounts—such as corporate email systems, financial institutions, or administrator-level network credentials—can command significantly higher prices. In some cases, entire corporate network access packages are sold to ransomware groups who then deploy extortion campaigns against the compromised organization. This layered ecosystem of specialization allows criminals to focus on their strengths, whether harvesting data, brokering access, or executing attacks.
Global Demand for Stolen Credentials
The market for stolen credentials is truly global, with buyers and sellers operating across multiple regions and jurisdictions. However, certain geographic areas have emerged as major centers of activity. Eastern Europe has historically been associated with sophisticated cyber-crime communities, particularly due to technical expertise and longstanding underground hacker forums that predate modern dark web marketplaces. These communities often develop advanced malware and exploit kits that fuel credential harvesting operations.
Demand is also strong in regions where cyber-crime enforcement resources are limited or legal frameworks are inconsistent. Southeast Asia, parts of Latin America, and segments of the Middle East have seen growing participation in underground marketplaces as both buyers and sellers. Meanwhile, the largest volume of stolen credentials often originates from users in North America and Western Europe, where high digital adoption rates and valuable financial systems make compromised accounts particularly lucrative targets.
Detection Strategies for Identifying Breached Credentials
Despite the sophistication of these marketplaces, organizations are not powerless against credential theft. One of the most effective defensive strategies is continuous monitoring for compromised credentials appearing on underground forums and dark web marketplaces. Specialized threat intelligence services scan these hidden platforms and alert organizations when employee email addresses or corporate domain credentials are discovered within breach datasets.
Technical defenses also play a crucial role. Multi-factor authentication dramatically reduces the effectiveness of stolen credentials because attackers must obtain additional authentication factors beyond the password itself. Behavioral monitoring systems can detect unusual login patterns, such as access attempts from unfamiliar geographic locations or devices. Credential exposure detection tools can also monitor password reuse across systems and automatically force resets when potential compromise is detected. Together, these strategies significantly reduce the operational value of stolen credentials in the underground economy.
Future Trajectory of Dark Web Cybercrime Marketplaces
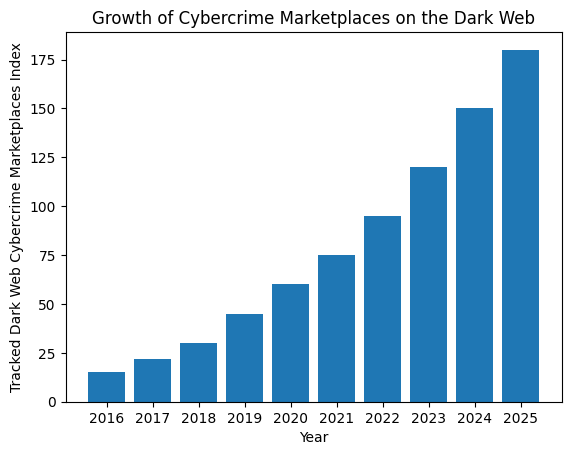
The trajectory of cyber-crime marketplaces suggests continued expansion and increasing sophistication. As artificial intelligence tools become more accessible, attackers may automate credential harvesting campaigns at unprecedented scale. AI-generated phishing messages, automated vulnerability scanning, and machine learning-powered password cracking could dramatically increase the volume of stolen credentials entering underground markets.
At the same time, marketplace operators are likely to continue refining their operational models to evade law enforcement disruption. Decentralized marketplace architectures, encrypted peer-to-peer trading systems, and invitation-only cybercrime communities are already emerging as alternatives to traditional centralized platforms. These developments suggest that the underground economy will continue evolving in response to both technological innovation and defensive efforts from the cybersecurity community.

Final Thoughts
The expansion of cyber-crime marketplaces reveals an uncomfortable truth about the digital world: identity itself has become a tradable commodity. A simple username and password combination can open doors to financial systems, corporate infrastructure, and personal lives. When aggregated at scale, these small fragments of information become powerful assets in a global criminal marketplace operating largely beyond the reach of traditional law enforcement.
Addressing this challenge requires more than improved technical defenses. It demands a fundamental shift in how digital identity is protected, managed, and monitored. Organizations must assume that credentials will eventually be compromised and design systems that remain secure even when authentication data is exposed. In a world where underground markets trade in access to the digital lives of millions, resilience—not secrecy—has become the most important principle of cybersecurity.

Subscribe to CyberLens
Cybersecurity isn’t just about firewalls and patches anymore — it’s about understanding the invisible attack surfaces hiding inside the tools we trust.
CyberLens brings you deep-dive analysis on cutting-edge cyber threats like model inversion, AI poisoning, and post-quantum vulnerabilities — written for professionals who can’t afford to be a step behind.
📩 Subscribe to The CyberLens Newsletter today and Stay Ahead of the Attacks you can’t yet see.







